In this article, discover the pivotal role of Terraform modules in enhancing reusability and optimizing Infrastructure as Code workflows.
Table of Contents
What is Terraform?
- It is an open-source IaaC (Infrastructure as a code) software tool where you define and create resources using providers in the declarative configuration language example JSON.
- With Terraform, You can package and reuse the code in the form of modules.
- It supports a number of cloud infrastructure providers such as AWS, Azure, GCP, IBM Cloud, OCI, etc.
What is Terraform Modules?
A Terraform module is a set of configuration code files with structured folder architecture. we create these modules to combine resources that are used for a specific single operation, which reduces the lines of code needed to create related infrastructure components.
What is DRY Principle in Terraform Modules?
- DRY Principle:
- Principle: Don’t Repeat Yourself (DRY) advocates for avoiding redundancy and duplication in code.
- Explanation: The goal is to minimize repetition by encapsulating common functionality in a modular and reusable way.
- DRY in Terraform Modules:
- Application: Terraform modules embody the DRY principle by allowing the creation of reusable configurations for infrastructure components.
- Implementation: Modules encapsulate resources and configurations, enabling the definition of infrastructure components once and reuse across projects without duplicating code.
- Benefits: Reduces redundancy, promotes consistency, and simplifies maintenance by managing common infrastructure patterns in a modular fashion.
What does a module do?
A Terraform module allows you to create logical abstraction on the top of some resource set. In other words, a module allows you to group resources together and reuse this group later, possibly many times.
Let’s assume we have a virtual server with some features hosted in the cloud. What set of resources might describe that server? For example:
- the virtual machine itself, created from some image
- an attached block device of a specified size for additional storage
- a static public IP mapped to the server’s virtual network interface
- a set of firewall rules to be attached to the server
- other things like another block device, additional network interface, and so on
Why use Terraform Modules?
A Terraform module allows you to create logical abstraction on the top of some resource set. In other words, a module allows you to group resources together and reuse this group later, also sharing the modules between teams or even in the community.
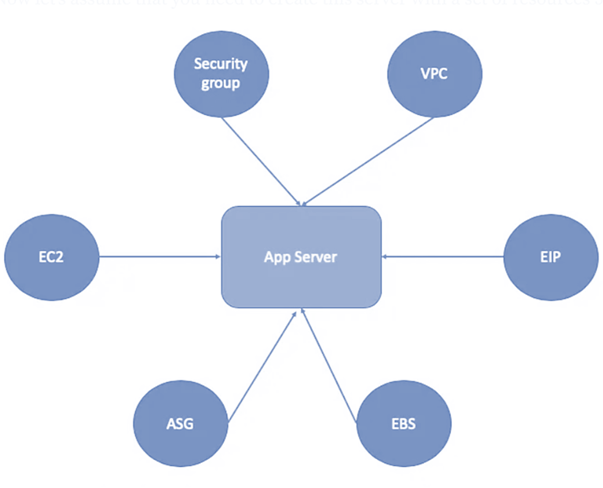
Assuming you have a EC2 server that hosted in AWS, what AWS resources this EC2 server is using?
- EC2 instance itself
- A EBS volume for store application data
- A elastic IP for public access
- A security group for ingress and egress traffic
- A VPC
- A Subnet
- ..etc
Module Components
A typical Terraform module consists of the following components:
- main.tf: This file contains the main configuration for the resources defined in the module.
- variables.tf: Defines input variables that users can customize when using the module.
- outputs.tf: Specifies output values that users can retrieve when the module is applied.
- README.md: Documentation detailing how to use the module, including variables, outputs, and any specific considerations.
Types of Terraform Modules
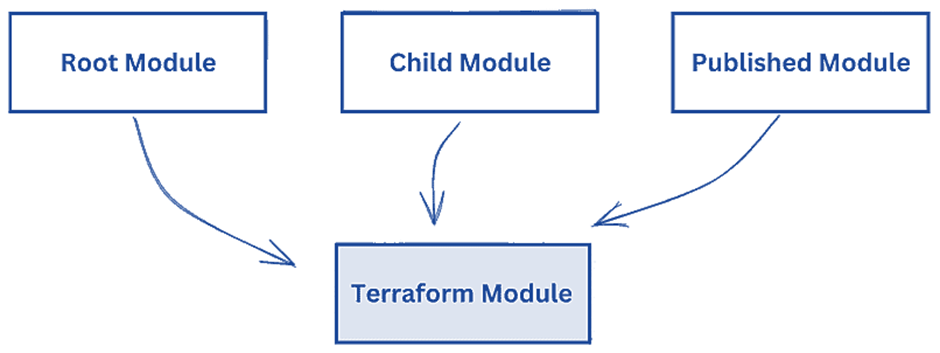
With Terraform, you are most likely to come across one of three main categories of modules:
Root Module
- The primary entry point for Terraform configurations.
- Contains the main configuration files, typically orchestrating the deployment of multiple resources.
- Serves as the top-level module in a Terraform project.
Child Module
- Subordinate modules encapsulated within the root module or other child modules.
- Focus on specific functionalities or resources, contributing to the modular structure of the infrastructure code.
- Enhances code organization and maintainability within the broader project.
Published Modules
- External modules shared and published for broader use.
- Created by the community or organizations to facilitate the reuse of well-designed infrastructure components.
- Accessed through various sources, such as the Terraform Registry, offering pre-built solutions for common infrastructure patterns.
Benefits of using Terraform Module
- Reusability: Modules enable the creation of standardized, reusable components that can be easily employed across different projects and environments.
- Abstraction: They provide a higher-level interface, abstracting complex infrastructure details and making it simpler for users to interact with and understand.
- Maintainability: By encapsulating resources and configurations, modules enhance code organization, making it easier to manage and update specific components without affecting the entire infrastructure.
- Collaboration: Facilitates teamwork by allowing teams to share and contribute to standardized infrastructure components, fostering a collaborative and efficient development process.
- Input Variables and Output Values: Supports customization through input variables and facilitates information retrieval via output values, adding flexibility and adaptability to modules.
- Granularity: Promotes a balanced granularity, ensuring that modules encapsulate specific functionality without becoming overly specialized or monolithic.
- Documentation: Enhances clarity and understanding through well-documented modules, describing usage, variables, and considerations, making them more accessible to users.
Potential Drawbacks of Terraform Modules
Despite the many benefits of Terraform modules, there are some caveats to consider:
Complexity
Modules can add complexity, especially when they are nested or highly parameterized. This complexity can make modules difficult to understand and maintain, particularly for larger teams and projects.
Versioning
Versioning modules can be a challenge. When a module is updated, you need to carefully manage the versions used in your different environments to avoid unwanted changes.
Flexibility vs. Standardization
While modules promote standardization, they may limit flexibility. A highly abstracted module may not cater to all use cases and could require changes to meet specific needs, which can undermine the principle of reusability.
Cloud Provider Support for Terraform Modules
Terraform boasts extensive support for various cloud providers, enabling users to manage infrastructure across multi-cloud and hybrid cloud environments.
The following cloud providers have official support for Terraform modules:
- Amazon Web Services (AWS): Terraform has robust support for AWS services, and numerous modules are available for provisioning resources such as EC2 instances, S3 buckets, and more.
- Microsoft Azure: Azure users can leverage Terraform modules to provision and manage resources like virtual machines, storage accounts, and networking components.
- Google Cloud Platform (GCP): Terraform modules facilitate the deployment of GCP resources, including compute instances, storage buckets, and networking configurations.
- Alibaba Cloud: Terraform supports Alibaba Cloud, enabling users to define and deploy resources in the Alibaba Cloud environment using modular code.
- Oracle Cloud Infrastructure (OCI): OCI users can use Terraform modules to define and deploy infrastructure components such as compute instances, block storage, and networking resources.
- DigitalOcean:
- Terraform includes a provider for DigitalOcean, allowing users to define and manage infrastructure resources on the DigitalOcean platform.
- VMware vSphere:
- Terraform provides a provider for VMware vSphere, enabling users to manage virtualized infrastructure on VMware platforms.
- OpenStack:
- Terraform supports OpenStack, allowing users to define and manage resources in OpenStack-based private or public clouds.
Use Cases of Terraform Modules
Here are some common use cases where Terraform modules shine:
- Network Infrastructure:
- Modules can be used to define networking components such as Virtual Private Clouds (VPCs), subnets, security groups, and routing configurations. This promotes modularity and reusability across different projects or environments.
- Compute Resources:
- Modules are well-suited for defining compute resources like virtual machines, containers, and serverless functions. They allow users to standardize configurations and easily deploy instances with consistent settings.
- Database Deployments:
- When deploying databases across different projects or environments, modules can encapsulate the configuration details. This includes parameters such as database engine, instance size, storage settings, and access controls.
- Load Balancers and Traffic Management:
- Modules can be used to define load balancers, traffic management rules, and CDN configurations. This ensures consistent setups for distributing traffic across multiple instances or regions.
- Monitoring and Logging:
- Modules are valuable for defining monitoring and logging configurations. This may include setting up alerts, log storage, and integration with monitoring tools, ensuring a standardized approach to observability.
- Security Policies:
- Modules are beneficial for encapsulating security policies and configurations. This includes defining IAM roles, access controls, encryption settings, and compliance requirements across different parts of your infrastructure.
- Identity and Access Management (IAM):
- Modules can simplify IAM configurations by encapsulating roles, policies, and permissions. This ensures that consistent access controls are applied across different projects or environments.
- Storage and Content Delivery:
- For managing storage solutions and content delivery networks (CDNs), modules can be employed. This includes defining object storage, file systems, and CDN configurations with consistent settings.
- Hybrid Cloud Deployments:
- In scenarios where infrastructure spans multiple cloud providers or includes on-premises components, modules can provide a unified approach to managing resources across diverse environments.
- Application Deployments:
- Modules are valuable for defining application deployments, especially in microservices architectures. Each module can encapsulate the necessary infrastructure, configurations, and dependencies for a specific application component.
- Environment-specific Configurations:
- Modules can be used to manage environment-specific configurations. For instance, a module could define development, staging, and production environments with appropriate settings for each.
- Compliance as Code:
- Modules are instrumental in implementing Compliance as Code. By encapsulating configurations that adhere to regulatory requirements, modules ensure that infrastructure is consistently deployed in a compliant manner.
- Custom Modules for Organization-specific Patterns:
- Organizations often have specific patterns or configurations that are repeated across various projects. Custom modules can be created to encapsulate these patterns, promoting consistency and adherence to organizational standards.
- Vendor-specific Integrations:
- Modules can encapsulate vendor-specific integrations, such as those for cloud services, APIs, or third-party tools. This facilitates the adoption of new services or tools across different parts of the infrastructure.
- Microservices Infrastructure:
- In a microservices architecture, each microservice can be encapsulated within its own module. This allows teams to independently manage and deploy their services while adhering to common infrastructure patterns.
Applying Terraform Modules Across Environments
- Development Environment:
- Purpose: Customize modules for rapid development and testing.
- Example: In the development environment, use smaller instance types and enable debugging features for faster iterations.
- Staging Environment:
- Purpose: Test integration with realistic configurations.
- Example: In the staging environment, adjust configurations for larger instance types and use more realistic resource settings.
- Production Environment:
- Purpose: Emphasize high availability, scaling, and security.
- Example: In the production environment, configure modules for larger instance types, auto-scaling groups, and stringent security measures.
Common Configuration Considerations:
- Variable Overrides:
- Purpose: Adjust configurations based on the environment.
- Example: Use conditional statements to set variables, e.g., choose instance types dynamically based on the environment.
- Terraform Workspaces:
- Purpose: Manage multiple environments within a single configuration.
- Example: Utilize Terraform workspaces to switch between development, staging, and production environments efficiently.
- Remote State Management:
- Purpose: Securely store and share Terraform state files.
- Example: Configure a backend, such as AWS S3, to store Terraform state files centrally, ensuring collaboration and consistency.
Basic infrastructure setup using Terraform Modules in AWS
Project Structure:
terraform-modules-example/
├── main.tf
├── variables.tf
├── outputs.tf
└── modules/
└── web_server/
├── main.tf
├── variables.tf
└── outputs.tfStep 1: Create the Web Server Module
modules/web_server/main.tf
provider "aws" {
region = var.region
}
resource "aws_instance" "web_server" {
ami = var.ami
instance_type = var.instance_type
tags = {
Name = var.server_name
}
}modules/web_server/variables.tf
variable "region" {
description = "AWS region"
}
variable "ami" {
description = "AMI for the web server"
}
variable "instance_type" {
description = "Instance type for the web server"
}
variable "server_name" {
description = "Name tag for the web server"
}modules/web_server/outputs.tf
output "web_server_ip" {
value = aws_instance.web_server.public_ip
}Step 2: Create the Main Configuration
main.tf
provider "aws" {
region = "ap-south-1"
}
module "web_server_instance" {
source = "./modules/web_server"
region = "ap-south-1"
ami = "ami-0287a05f0ef0e9d9a" # Example AMI ID
instance_type = "t2.micro"
server_name = "web-instance"
key_name = "three-tier"
}variables.tf : # No variables defined for the main configuration
outputs.tf
output "web_server_ip" {
value = module.web_server_instance.web_server_ip
}Methods for using Terraform modules
- Local Module Sources:
Method:
module "example" { source = "./modules/example" }Explanation:
Modules can be defined locally within the same Terraform configuration by specifying a local file or directory path as the source.
This method is useful for creating project-specific modules or when developing custom modules that are closely tied to the main configuration.
- Git Module Sources:
Method:
module "example" { source = "git::https://github.com/example/modules.git//example" }Explanation:
Modules can be sourced from Git repositories by providing the Git repository URL and the path within the repository where the module is located.
This method is beneficial for reusing modules across different projects or teams and maintaining version control.
- Terraform Registry Module Sources:
Method:
module "example" { source = "hashicorp/example/module" }Explanation:
Modules can be sourced directly from the Terraform Registry, a public repository of pre-built Terraform modules.
This method simplifies module usage by eliminating the need to manage external Git repositories and allows for easy discovery of modules.
- Module Variables:
Method:
module "example" { source = "./modules/example" var1 = "value1" var2 = "value2" }Explanation:
Modules often expose variables that can be customized when the module is used. These variables allow users to pass specific values to the module, influencing its behavior.
This method enables flexibility and reusability as the same module can be used with different configurations.
- Module Outputs:
Method:
output "output_value" { value = module.example.output_variable }Explanation:
Modules can define output variables, and these outputs can be referenced in the main configuration. This allows the main configuration to consume and use values calculated or produced by the module.
Outputs facilitate communication between the main configuration and the module.
- Module Versioning:
Method:
"example" { source = "git::https://github.com/example/modules.git//example" version = "v1.2.0" }Explanation:
Modules can be versioned to ensure stability and consistency. Version constraints can be specified to control which version of the module is used.
This method is crucial for managing dependencies and ensuring that changes to modules do not unintentionally impact infrastructure.
Conclusion:
Terraform modules are a powerful tool for managing your infrastructure as code. They provide reusability, consistency, and organization, helping to streamline infrastructure deployment and management. However, it’s important to strike a balance between the abstraction provided by modules and the unique needs of your infrastructure. A careful and considered use of Terraform modules is required to successfully improve your workflow.
Reference:-
For reference visit the official website TerraformRegistry.
Any queries pls contact us @Devopshint.
Related Articles:
Terraform State File Management | Terraform Local State File | Terraform Remote State